Intruder Releases the Security Middle Child Report, Revealing How the Cybersecurity Industry Is Leaving Midmarket Businesses Behind
#attacksurfacemanagement--Intruder, a leader in exposure management, today released its Security Middle Child Report, which uncovered that almost half of cybersecurity leaders at midmarket businesses,...
Research of US and UK Midmarket Cybersecurity Leaders Showcases How Midmarket Organizations Project Cyber Confidence, But Many Teams Are Stretched and Lack Appropriate Solutions
- 94% are confident in their ability to identify and remediate critical risks before attackers exploit them, but there are cracks underneath that confidence. For example, 42% describe their team as either stretched, overwhelmed or consistently behind
- 46% say enterprise platforms assume more staff, budget, or complexity than they can support and 29% say SME tools no longer meet their needs. They’re not failing to use the right tools as the right tools largely don't exist for them
- 51% of respondents say it would take approximately a week to assess their exposure to a critical zero-day. In a threat landscape where exploitation can follow disclosure within 24-48 hours, a week is too long
LONDON: #attacksurfacemanagement--Intruder, a leader in exposure management, today released its Security Middle Child Report, which uncovered that almost half of cybersecurity leaders at midmarket businesses, e.g. companies with at least $50M revenue and between 400-6000 employees, say they don’t have the right technology solutions, leaving them stuck in what Intruder calls the “security middle child problem." 46% say enterprise platforms assume more staff, budget, or complexity than they can support and 29% say SME tools no longer meet their needs. As a result of these poor fits, 42% describe their teams as either stretched, overwhelmed or consistently behind.
Midmarket companies represent a core component of the US economy. JP Morgan Chase & Co. estimates that segment consists of approximately 300,000 businesses generating $13T in annual revenue and employs over 40 million people within the US alone. Despite its importance, Intruder’s research shows how the cybersecurity vendor market is not adequately serving the midmarket - leaving teams with limited visibility into what's exposed (28%), too many tools to navigate (26%), and struggling to prioritize (24%).
“Midmarket companies are being treated as the middle child when it comes to cybersecurity solutions. They are overlooked by vendors focused on Fortune 500s or SMBs, while they are just as important and just as vulnerable to attackers,” said Chris Wallis, CEO and founder of Intruder. “This is a structural problem, the majority of solutions available to midmarket security teams were never built for the position they're now in.”
Cybersecurity leaders claim to feel confident and in control, but cracks are showing
Midmarket security leaders defy the stereotype of an overworked, underfunded team. 89% report increasing budgets. Around 70% say headcount has kept pace with their digital estate. 64% feel their posture scaled appropriately with growth. 94% are confident in their ability to identify and remediate critical risks before attackers exploit them while 51% are "very confident."
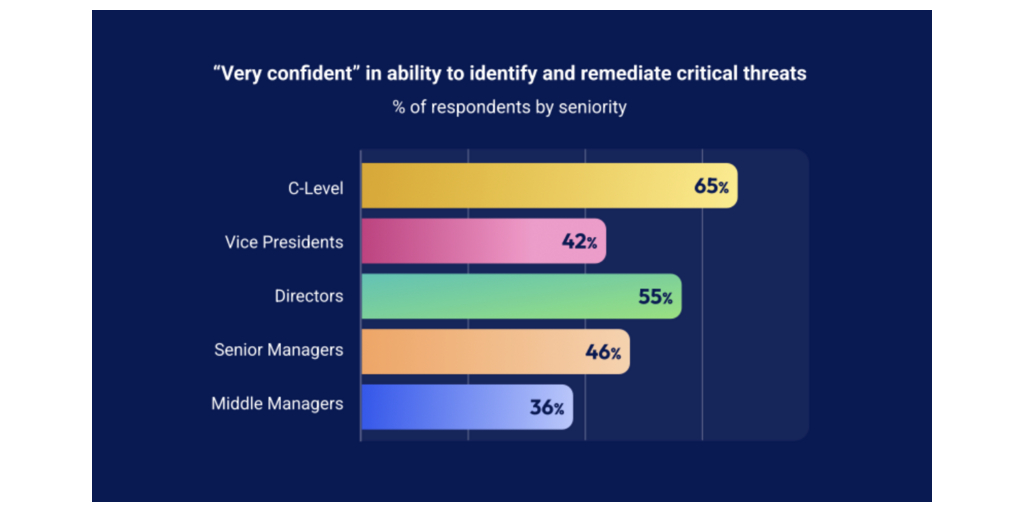
But dig beneath those numbers and cracks appear. 65% of C-suite respondents are very confident in their ability to catch critical threats, but that drops sharply among those closer to the actual work: Directors at 55%, Senior Managers at 46%, and Middle Managers at 35%. The further you are from the coalface, the more confident you are.
One major concern is that 51% of respondents say it would take approximately a week to assess their exposure to a critical zero-day. In a threat landscape where exploitation can follow disclosure within 24-48 hours, a week is too long.
Midmarket digital estates are growing while teams are feeling strained
91% of respondents say their digital estate grew over the past 24 months and 38% say it grew significantly. While many teams responsible for securing that estate are growing with it, a large portion are lagging behind: only 30% of organizations grew headcount faster than their digital estate, 17% grew more slowly, and nearly 10% stayed flat. That gap has a human cost. 41% reported their teams are dealing with feelings of strain: 21% say they are stretched but coping, 11% feel overwhelmed and stuck in a reactive mode, and 9% are consistently behind and exposed.
36% of respondents acknowledge their security posture hasn't scaled appropriately with digital estate growth. For 14%, that gap won't close for at least another six months. However, only 17% are prioritizing headcount this year. The dominant investment priorities are AI and automation (49%) and adding new solutions (33%) - suggesting security leaders are reaching for technology to compensate for people. The data suggests this isn't working: 44% describe a stack that is either outgrown or fragmented.
The pressure isn't evenly distributed. Healthcare shows the most strain - only 51% kept headcount at pace with their digital estate, and 26% grew more slowly. In SaaS, that figure rises to 86%, with only 10% growing more slowly. The gap is striking in healthcare given the stakes involved.
Current tech solutions aren’t meeting their needs
44% of teams have either outgrown their stack or stitched it together from point solutions that don't provide a unified view. This has a cost: 26% cite navigating too many security tools as a top challenge, 24% cite too many alerts with poor prioritization, and 20% cite the inability to measure and report on cyber hygiene. The stack isn't just complex - it's actively getting in the way. And with 33% planning to add more solutions this year, the fragmentation is likely to deepen.
Underpinning this is a vendor market that isn't built for the midmarket. 46% say enterprise platforms assume more staff, budget, or complexity than they can support. 29% say SME tools no longer meet their needs. Midmarket teams aren't failing to use the right tools. It’s that the right tools largely haven't existed for them.
41% of respondents report using AI pentesting, and it appears in the top five most-adopted tools for fintech, manufacturing, and retail. Given the category only emerged 12-18 months ago, it's unclear whether teams are using true AI pentesting or applying the term more loosely. But the intent is clear: nearly half (49%) cite AI and automation as their top investment priority for 2026, suggesting security leaders are looking to AI to help them do more with less.
That said, AI pentesting only breaks into the top five for organizations with $500M+ revenue - implying it’s currently most accessible to companies with the most resources. Adoption also increases with team size: 49% of organizations with 11+ security staff report using it, versus just 25% of teams with 2-5 people. For the smallest, most stretched teams AI is supposed to help, do existing solutions risk adding complexity rather than relieving pressure?
Cyber risk isn't a boardroom conversation
Despite growing digital estates, an increasing frequency of high-profile breaches, and signs that security posture is struggling to keep pace, cyber risk remains largely below the boardroom. Only 9% discuss cyber risk at board level. 34% reach executive leadership. The majority (51%) keep it at security/IT leadership only, and 7% confine it to the security team alone.
“The data in this report doesn't point to a single problem. It points to four compounding ones: estates growing faster than teams, confidence highest where visibility is lowest, stacks that are increasingly fragmented. And the relevant conversations aren’t reaching the people who need to hear it,” says Dan Andrew, head of security at Intruder. “Until that changes, the gap between how these teams present themselves and how they actually operate will keep widening.”
Organizations interested in reviewing the full Security Middle Child Report can find it for download here. Security and IT teams interested in learning more about the Intruder platform can book an introductory call here.
About This Survey
The research was conducted by Censuswide among 502 CISOs and equivalent decision makers (Managers, Directors, Leads, VPs and CISO-equivalents) surveyed across the UK (200) and US (302) between February 11–18, 2026, at organizations with 400-6,000 employees and at least $50 million revenue, across financial services, fintech, healthcare, manufacturing, professional services, retail and SaaS. Censuswide abides by and employs members of the Market Research Society and follows the MRS code of conduct and ESOMAR principles. Censuswide is also a member of the British Polling Council.
About Intruder
Intruder’s exposure management platform helps lean security teams stop breaches before they start by proactively discovering attack surface weaknesses. By unifying attack surface management, cloud security and continuous vulnerability management in one intuitive platform, Intruder makes it easy to stay secure by cutting through the noise and complexity. Founded in 2015 by Chris Wallis, a former ethical hacker turned corporate blue teamer, Intruder is now protecting over 3,000 companies worldwide. Learn more at https://intruder.io.
Q&A: Intruder’s Security Middle Child Report
Q: What is the Security Middle Child Report?
Intruder, a leader in exposure management, today released its Security Middle Child Report, a survey of over 500 CISOs and equivalent decision makers (Managers, Directors, Leads, VPs and CISO-equivalents) across the UK and US. It unveils how the cybersecurity vendor landscape isn't built to meet midmarket enterprise needs. Almost half (41%) of cybersecurity leaders at midmarket enterprises describe their teams as stretched, overwhelmed or consistently behind. A major contribution to this issue is how they don’t have the right technology solutions to support themselves: 46% say enterprise platforms assume more staff, budget, or complexity than they can support and 29% say SME tools no longer meet their needs.
Q: What does the Security Middle Child Report uncover about midmarket cybersecurity leaders’ confidence?
Midmarket security leaders defy the stereotype of an overworked, underfunded team and project high levels of confidence while overseeing increasing budgets. But that may be a facade as research shows they have low visibility into crucial security needs, slow response times to critical zero-days and more.
Q: What does the Security Middle Child Report uncover about midmarket cybersecurity leaders’ technology investments?
89% report increasing budgets but it’s unclear if that money is invested wisely. Almost half are prioritizing AI/automation adoption, choosing new, untested technology over best-practices such as cyber hygiene training for non-cybersecurity employees (31%), professional development/certification/training for existing team members (28%) or increasing compliance & governance with new regulatory bodies (23.5%).
Q: What does the Security Middle Child Report uncover about midmarket cybersecurity leaders’ current cybersecurity technology stacks?
Midmarket security stacks are fragmented, with no clear consensus on what good looks like. No single tool breaks above 56% adoption. CSPM leads at 55%, followed by SIEM (47%), WAF (47%), DSPM (44%), and EDR/XDR (43%). Not only is the stack fragmented, it's actively making the job harder. 24% of respondents cite too many alerts with poor prioritization as a top challenge, and 26% cite navigating too many security tools.
Q: What does the Security Middle Child Report uncover about midmarket companies’ prioritization of cybersecurity risks?
Despite growing digital estates and signs that security posture is struggling to keep pace, cyber risk remains largely below the boardroom. Only 9% discuss cyber risk at board level. 34% reach executive leadership. The majority (51%) keep it at security or IT leadership only, and 7% confine it to the security team alone. A lack of board reporting signals that most midmarket organizations haven't yet connected cybersecurity to business risk.
Fonte: Business Wire
Related news
Last News
RSA at Cybertech Europe 2024
Alaa Abdul Nabi, Vice President, Sales International at RSA presents the innovations the vendor brings to Cybertech as part of a passwordless vision for…
Italian Security Awards 2024: G11 Media honours the best of Italian cybersecurity
G11 Media's SecurityOpenLab magazine rewards excellence in cybersecurity: the best vendors based on user votes
How Austria is making its AI ecosystem grow
Always keeping an European perspective, Austria has developed a thriving AI ecosystem that now can attract talents and companies from other countries
Sparkle and Telsy test Quantum Key Distribution in practice
Successfully completing a Proof of Concept implementation in Athens, the two Italian companies prove that QKD can be easily implemented also in pre-existing…
Most read
Zayo Issues $2.37 Billion of Asset-Backed Term Notes
Zayo, a leading digital infrastructure provider, today announced it has closed on the issuance of $2.37 billion of asset-backed term notes (the “Notes”),…
Mitek to Report Fiscal 2026 Second Quarter Financial Results on May 7,…
Mitek Systems, Inc. (NASDAQ: MITK), a global leader in digital identity verification and fraud prevention, today announced that it will release its financial…
Orkes Raises $60M as Developers Increasingly Use Its Platform to Deploy…
Orkes, the agents and durable workflow orchestration platform built by the original architects of Netflix's microservices orchestration platform, has…
Hitachi Digital Services Announces Strategic Partnership with Stripe to…
#AI--Hitachi Digital Services, the global systems integrator powering mission-critical platforms, today announced a strategic partnership with Stripe,…






